This lab series guides you from the initial deployment of pfSense. Then, it progresses to advanced configurations. It provides a structured, step-by-step journey through every major feature. If you missed any of the other parts, they are linked below. This way, you can catch up and get the most from the full lab experience.
- pfSense Series: Simple Setup & Introduction
- pfSense Lab Part 2: Master pfBlockerNG Package
- Deploying pfSense: Complete Lab Series Part 3 – IDS/IPS With Snort
- pfSense Lab Part 4: Captive Portal with AD
- Secure Your Network with pfSense and Squid Proxy
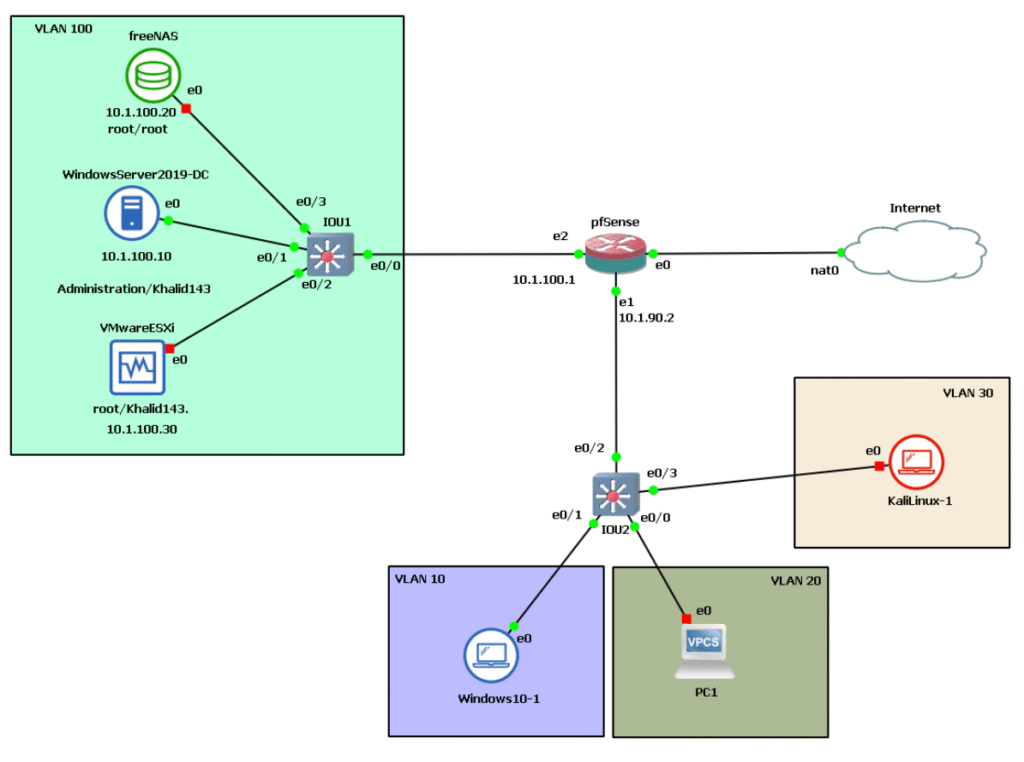
As a reminder, here’s the architecture below we’re working with.
In this post, you will learn about the concept of proxy servers, how they function, and why they are essential for network administration. We will also introduce Squid, a popular open-source caching and forwarding proxy that integrates seamlessly with pfSense.
What is a Proxy Server?
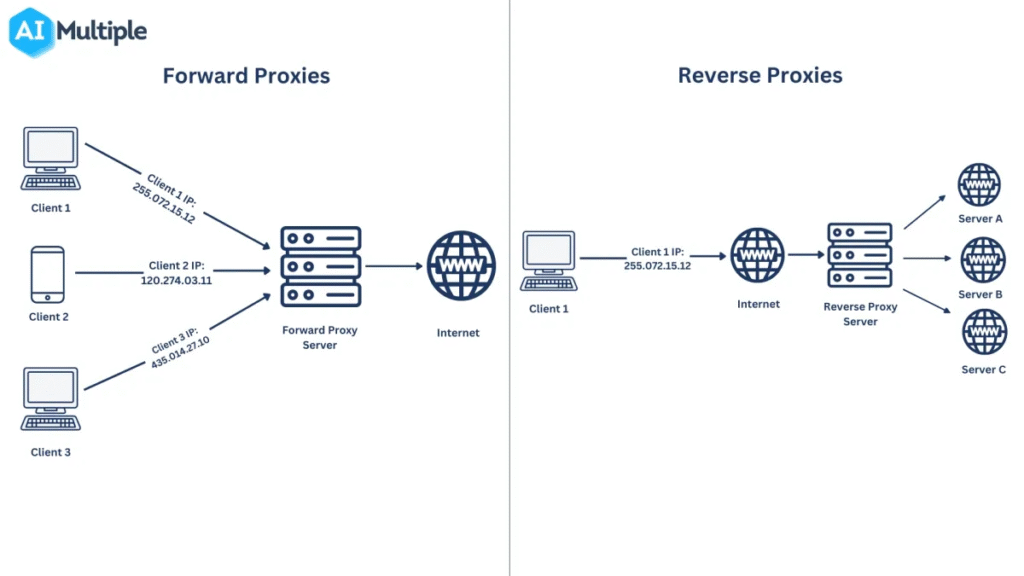
A proxy server acts as a gateway or intermediary between the end user and the internet. It separates user devices from the websites they visit, serving as a middleman that handles requests and responses. Proxy servers provide varying levels of functionality, security, and privacy based on organizational policies and user needs.
How Does a Proxy Server Work?
When you send a web request (like typing a URL in your browser), the request is first sent to the proxy server instead of directly to the website. The proxy then makes the request to the website on your behalf, collects the response (the web page or data), and sends it back to you.
This enables the proxy to:
- Modify or filter the request or response (for example, block certain websites or content).
- Hide your original IP address by replacing it with its own IP, enhancing user anonymity.
- Cache frequently visited pages to speed up performance for subsequent requests.
- Enforce company policies on internet usage like restricting access to certain categories of websites.
- Log and monitor user activity to improve security or compliance.
- Provide a firewall layer that protects internal networks from internet threats.
Why Should We Use a Proxy Server?
There are several reasons why organizations and individuals use proxy servers:
- Control Internet Usage: Organizations deploy proxy servers to monitor and control how employees use the internet. They can log all web requests to track browsing time and activities, even if sites are not blocked.
- Bandwidth Savings and Improved Speeds: Proxy servers cache popular websites locally. When you request a site, the proxy serves the cached copy if it is up-to-date, reducing bandwidth use and enhancing load times.
- Privacy Benefits: Proxies help users and organizations browse the internet more privately by masking IP addresses and anonymizing requests.
- Enhanced Security: Proxy servers add an additional security layer protecting internal networks. They can filter unwanted content, block malicious sites, and, when combined with VPNs, provide secure remote access to company resources.
In summary, proxy servers are essential tools for organizations to optimize network performance, improve security, and maintain control over internet use.
Types of Proxy Servers
Not all proxy servers operate the same way. Understanding the specific functionality of each type is important for choosing the right one for your needs:
- Transparent Proxy
Transparent proxies inform websites that they are proxy servers and always forward your real IP address, meaning the website can still identify you. These are often used to enforce corporate policies without changing user experience. - Anonymous Proxy
An anonymous proxy identifies itself as a proxy but does not disclose the user’s real IP address to the website. This helps protect user identity and keeps browsing habits private. - Distorting Proxy
A distorting proxy sends a false IP address while still identifying as a proxy. It adds another layer of obscurity between the user and the website. - High Anonymity Proxy (Elite Proxy)
High anonymity proxies periodically change the IP address they present to the website, making it extremely difficult to track which traffic belongs to which user. Examples include the TOR network, which offers the highest level of privacy and security online.
Squid
Squid is a powerful caching proxy server available as a package for pfSense that supports multiple protocols like HTTP, HTTPS, and FTP. It helps to reduce bandwidth usage and speeds up response times by caching frequently requested web content locally. This means that when users request the same web pages repeatedly, Squid serves the cached versions instead of fetching them from the original web servers, significantly improving performance and reducing internet traffic.
Beyond caching, Squid offers extensive access control features allowing administrators to define who can access what web content, and when. It functions as a great web accelerator and enhances security by filtering requests and blocking unwanted or harmful sites. Squid supports transparent proxy modes where users do not need to configure browsers to use the proxy manually, making deployment easier in corporate networks.
In pfSense, Squid configuration includes setting cache size and location, defining interfaces on which the proxy listens, enabling logging, and managing Access Control Lists (ACLs) for traffic regulation. Additional packages like SquidGuard extend Squid’s capability by adding category-based URL filtering and blacklisting, allowing granular control of web content access.
Overall, Squid in pfSense provides a comprehensive proxy solution to optimize internet usage, enforce web policies, and improve network efficiency and security.
Note: It is important to stay updated about security advisories related to Squid, as recent reports indicate some vulnerabilities; always ensure the use of secure, maintained versions.
Installing the Squid services on pfSense
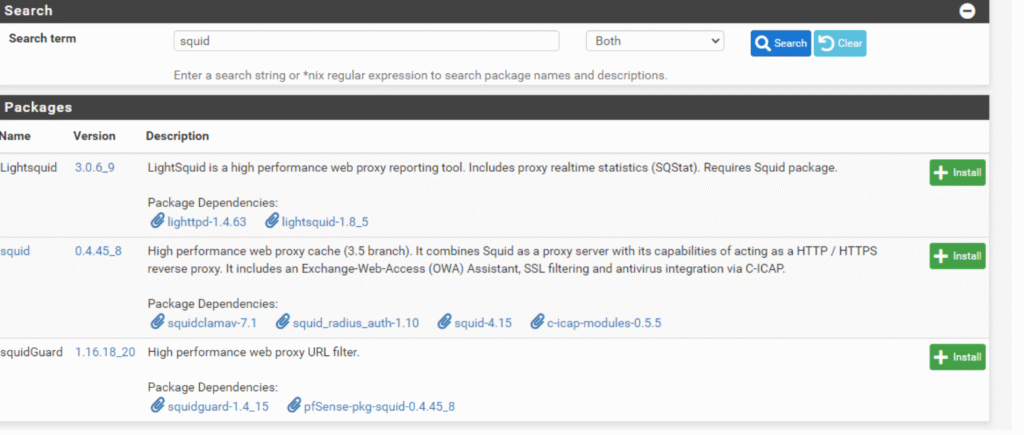
Squid is a caching proxy for HTTP and other protocols included in pfSense packages. It improves web browsing by locally caching frequently visited sites and objects, speeding access and saving bandwidth by reducing duplicate downloads. Squid also supports advanced traffic management including access control and reporting.
SquidGuard extends Squid by providing domain- or URL-based access control, allowing administrators to accept or block access based on client or destination. Blocked sites redirect users to error pages, and custom or external blacklists can be used.
- Filters access based on domain names and URLs.
- Permits or denies access depending on client and destination.
- Redirects blocked sites to custom error pages.
- Uses custom and pre-built blacklists.
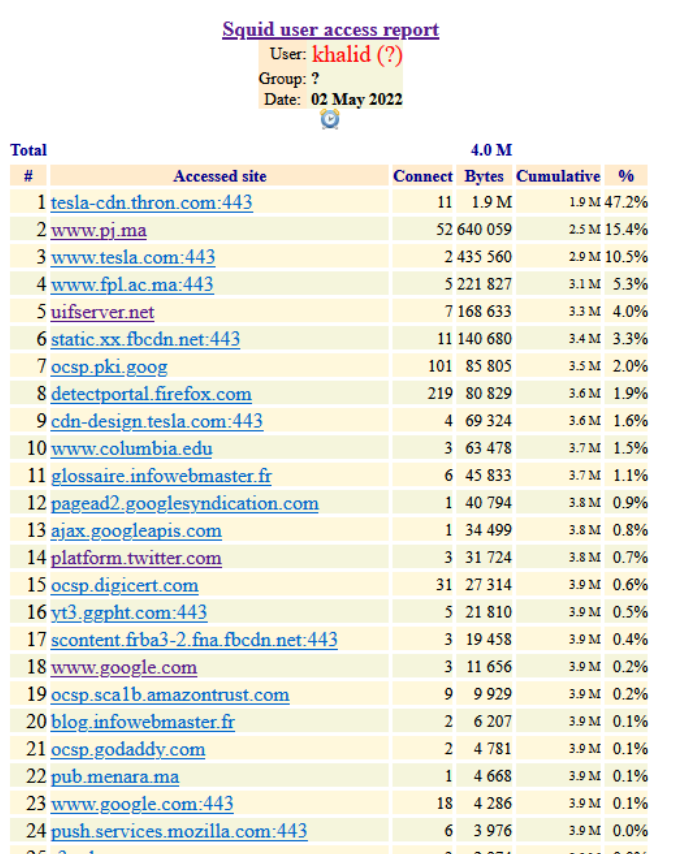
Lightsquid analyzes Squid logs to report web access history, detailing who visited which sites, bandwidth usage, and generates daily and monthly usage reports for monitoring purposes.
- Analyzes Squid access logs.
- Reports user web browsing history and bandwidth usage.
- Generates detailed periodic reports (daily, monthly).
Together, these tools offer comprehensive web optimization, control, and monitoring within pfSense networks.
Squid Configuration
Configuring Squid in pfSense involves several key steps to ensure the proxy service operates efficiently and reliably, especially in environments requiring high availability.
- Enable the Squid proxy service to activate it on your pfSense firewall.
- Select the network interface(s) to which the Squid proxy server will bind and listen for traffic; typically, this is the LAN interface or other internal networks.
- Choose the port on which Squid will listen for proxy requests, with the default usually being 3128.
- Configure CARP (Common Address Redundancy Protocol) settings if you have a master/backup pfSense setup to provide high availability, so the proxy service continues uninterrupted in case of failover.
- Additional settings include defining caching parameters, access control lists, logging preferences, and optional HTTPS interception for SSL filtering.
- It is critical to configure at least the local cache size; otherwise, Squid may fail to start.
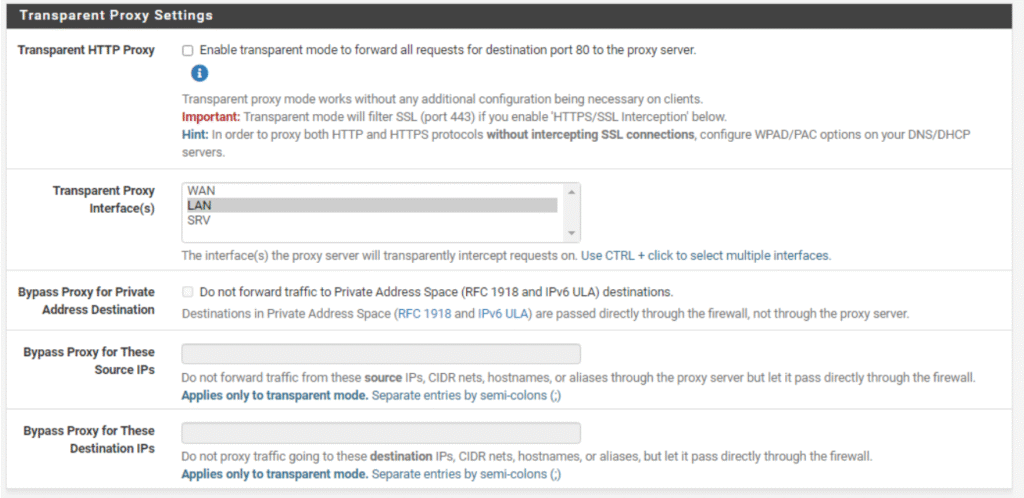
A transparent proxy works by intercepting and redirecting all client traffic through the proxy server automatically, without requiring any configuration on the client devices. This makes it convenient because users don’t have to manually set proxy settings in their browsers or applications. However, in pfSense, when transparent proxy mode is enabled, authentication features cannot be used because the users are not explicitly connecting through the proxy; their traffic is simply redirected transparently.
In our case, transparent proxy mode was disabled to allow for user authentication. This means users must explicitly authenticate before accessing the web, which is necessary for tracking, logging, or restricting access based on user credentials. Without disabling transparent proxy, setting up authentication like LDAP or local user database is not feasible.
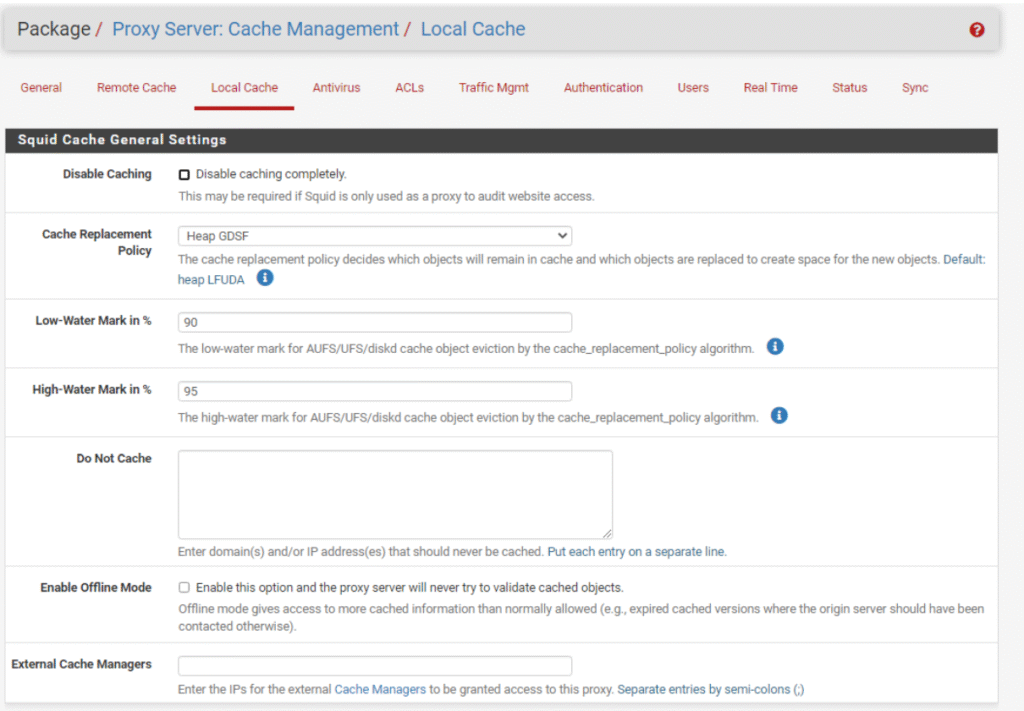
Configuring Local storage
Configuring the local storage for Squid on pfSense is a critical step to ensure the proxy server functions properly by caching web pages and objects efficiently. The local cache is where Squid stores these pages for quick retrieval, speeding up access and reducing bandwidth usage.
You can define several parameters for this cache:
- Whether the cache is stored on the hard disk or in RAM, depending on your system capabilities and performance needs.
- The cache storage mechanism, which involves how Squid organizes and manages cached data on disk.
- The maximum sizes of individual objects that can be stored, balancing between caching efficiency and resource utilization
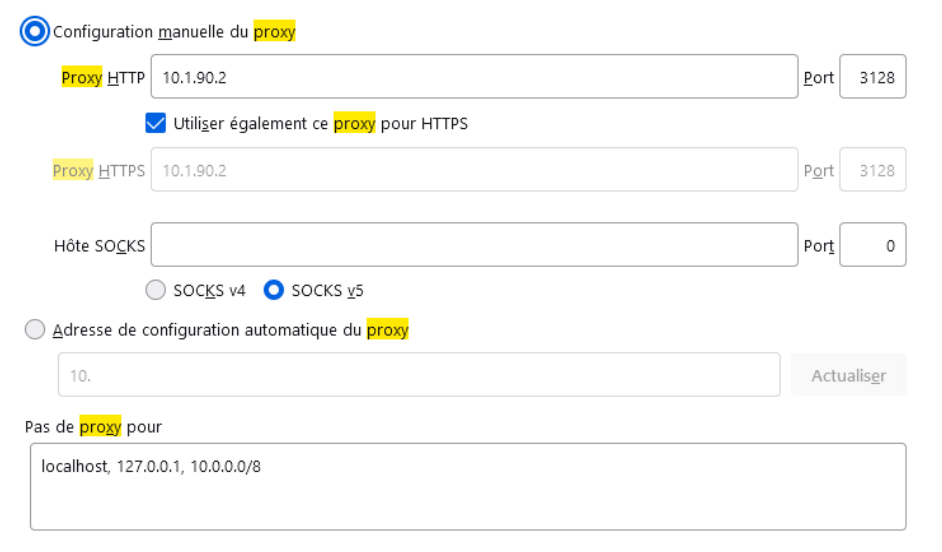
Another configuration should be made, which is configuring the browser to point to our proxy servers. For example, in Firefox:
- Open the Firefox menu and select “Settings” or “Options.”
- Scroll down to the “Network Settings” section.
- Click on the “Settings…” button.
- Choose “Manual proxy configuration.”
- Enter the IP address or hostname of your proxy server in the “HTTP Proxy” field.
- Specify the port number your proxy listens on (default is usually 3128).
- Optionally check “Use this proxy server for all protocols” to apply settings to HTTP, HTTPS, FTP, etc.
- Specify any websites to bypass the proxy in the “No proxy for” field.
- Click OK to save.
This step is essential to ensure that the browser sends its internet requests through the configured pfSense proxy server to benefit from caching, filtering, and other proxy functionalities.
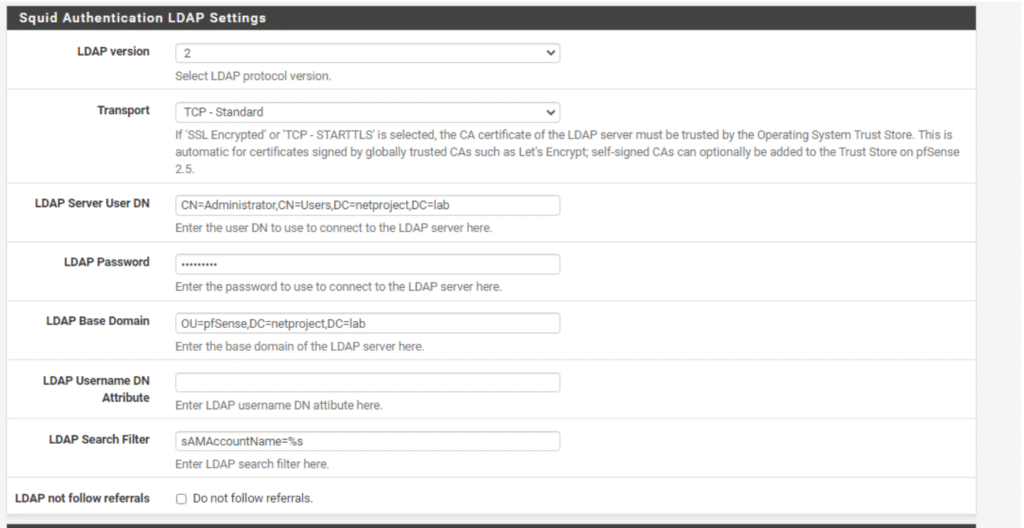
Squid Authentication through Active Directory
Another configuration should be made, which is setting up authentication with Active Directory. The idea behind this step is to ensure that only users stored in the pfSense organizational unit (OU) are allowed internet access via the proxy. This setup ties proxy access control directly to Active Directory user accounts, providing centralized management and security.
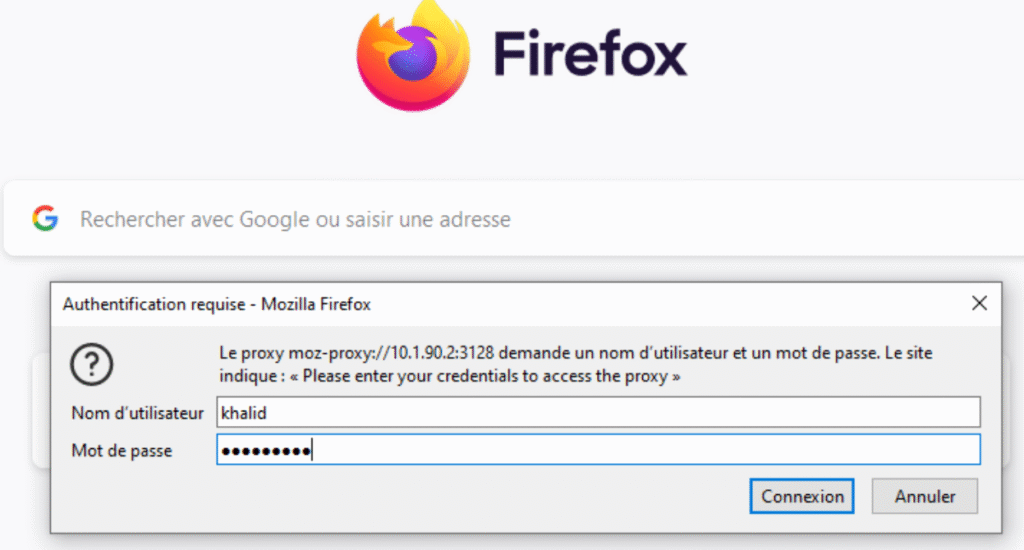
Authentication
The last step in setting up authentication with the proxy involves that whenever a user connects to the network, a pop-up window appears asking them to enter their credentials for authentication. This ensures that only authorized users, as defined in your Active Directory or local user database, can access the internet through the proxy server.
This pop-up authentication provides a secure and controlled environment by verifying user identity before allowing web access, aligning network access with organizational security policies.
Squid Integration with Antivirus ClamAV
ClamAV is an open-source antivirus engine designed to detect viruses, malware, trojans, and other malicious threats. In the context of proxy servers like Squid used with pfSense, ClamAV plays a crucial role in scanning and filtering web traffic in real-time to prevent infected files from entering the network.
For our use case, integrating ClamAV with the proxy server enhances network security by:
- Scanning incoming and outgoing web content for viruses and malware.
- Blocking or quarantining infected files before they reach user devices.
- Protecting the network from potential threats that propagate through HTTP, HTTPS, FTP, and other protocols.
- Complementing access control and filtering provided by Squid and SquidGuard with active threat detection.
This integration ensures comprehensive protection by combining proxy caching and filtering with robust antivirus scanning, maintaining a safer browsing environment.
Key points about ClamAV integration:
- ClamAV is an open-source antivirus engine widely used in network security.
- It scans web traffic passing through the Squid proxy in real-time.
- Helps block malicious files before they reach client devices.
- Supports scanning of multiple protocols including HTTP, HTTPS, and FTP.
- Complements proxy access control with malware detection.
- Essential for maintaining secure and clean network traffic in proxy setups.
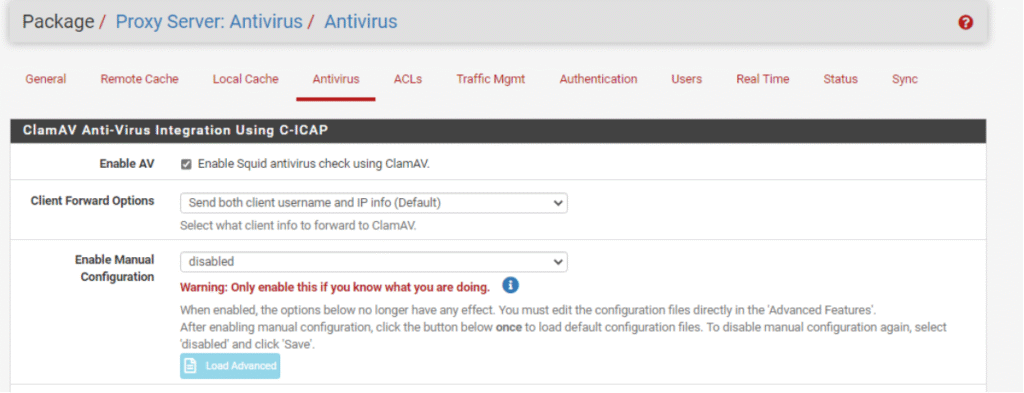
To enable the antivirus ClamAV in pfSense proxy:
- Go to the Antivirus tab within the Squid proxy settings.
- Enable the option Squid antivirus check using ClamAV.
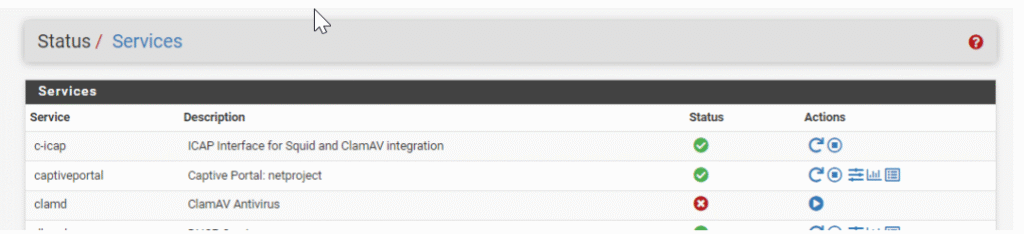
- Then, launch the ClamAV service to start virus scanning.
SquidGuard
SquidGuard is a URL redirection software used to control access to websites. It operates as a plugin for Squid and uses blacklists to define sites for which access is redirected. Ready-to-use, moderated blacklists can be downloaded from the internet; these blacklists filter websites by categories.
Key points about SquidGuard configuration:
- Acts as a URL redirector integrated with the Squid proxy.
- Controls user access to websites by using blacklists.
- Uses pre-moderated blacklists downloadable from the internet.
- Filters websites by categorizing them for targeted blocking.
- Supports redirecting blocked sites to informational pages.
- Enables granular control over web content access.
This system enhances network security and management by enforcing web usage policies based on categorized lists of allowed or blocked sites.
We can download ready-made, moderated blacklists from the Internet. These are ready-to-use blacklists that filter websites by category.
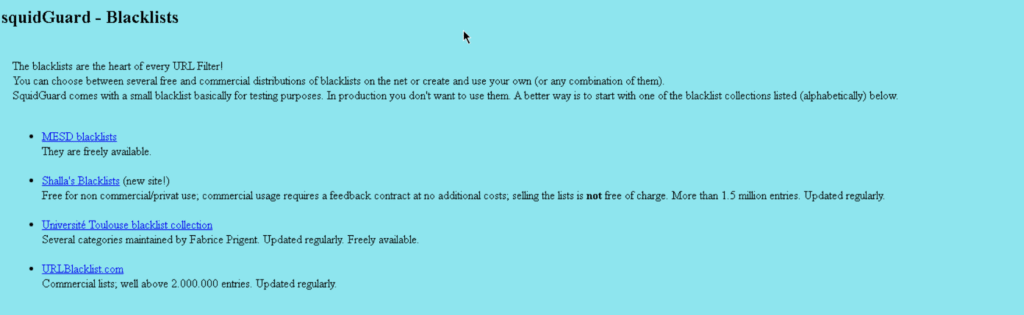
Here is the recommended blacklist recommended by Netgate. (http://www.squidguard.org/blacklists.html)
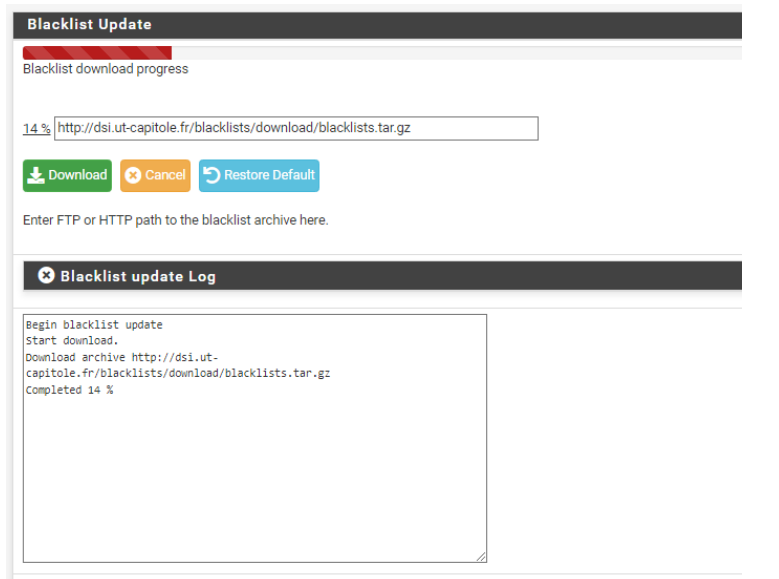
In my case, I use a blacklist moderated by the University of Toulouse.
(http://dsi.ut-capitole.fr/blacklists/download/blacklists.tar.gz)
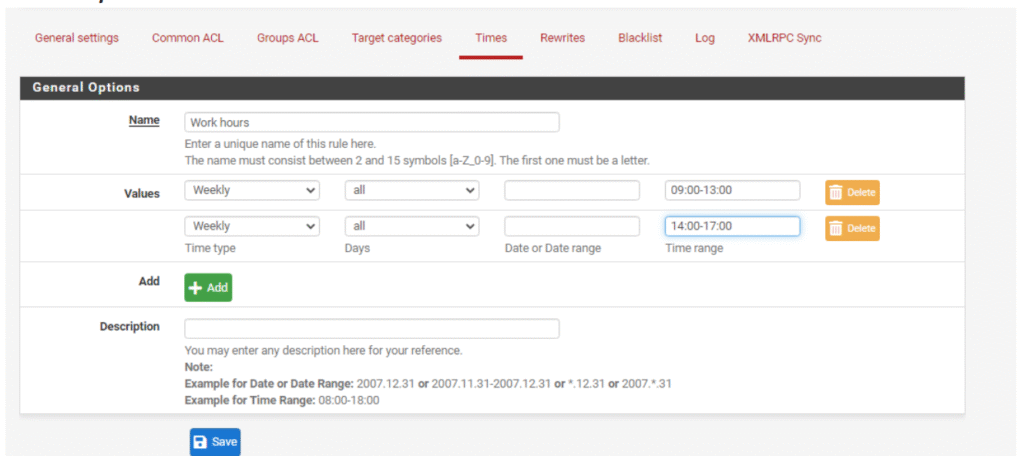
Schedule Setup with SquidGuard in pfSense
Schedule setup in SquidGuard allows you to enforce web access policies at specific times. This is particularly useful for controlling when users can access certain types of content, such as social media sites, during work hours.
By defining time-based rules, administrators can automatically block or allow access to specific websites or categories based on time periods like days of the week and specific hours. For example, social media sites can be restricted during office hours to enhance productivity, while remaining accessible outside of these hours.
Key points about schedule setup in SquidGuard:
- Schedules specify the time frames when filtering rules apply.
- They enable automated blocking or access permissions based on time.
- Administrators can restrict access to distracting or non-work related sites during work hours.
- Time ranges can include specific days, hours, and date ranges.
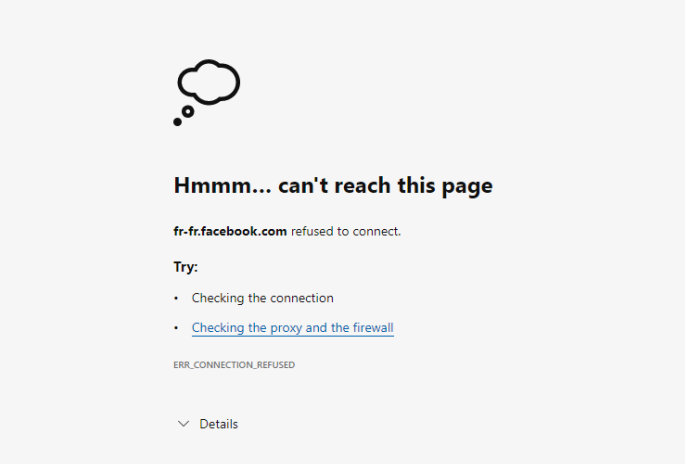
Creating an ACL to Block Social Media During Work Hours
To manage web access effectively, you can create an Access Control List (ACL) that prevents users from accessing social media sites during working hours. Using prepared category lists, such as those from the Toulouse collection, allows you to easily block specific types of websites based on categorization.
This ACL can be linked to defined schedules so that the blocking only applies during your specified work hours. Outside these hours, access to social media can be allowed, providing flexibility while maintaining productivity during the day.
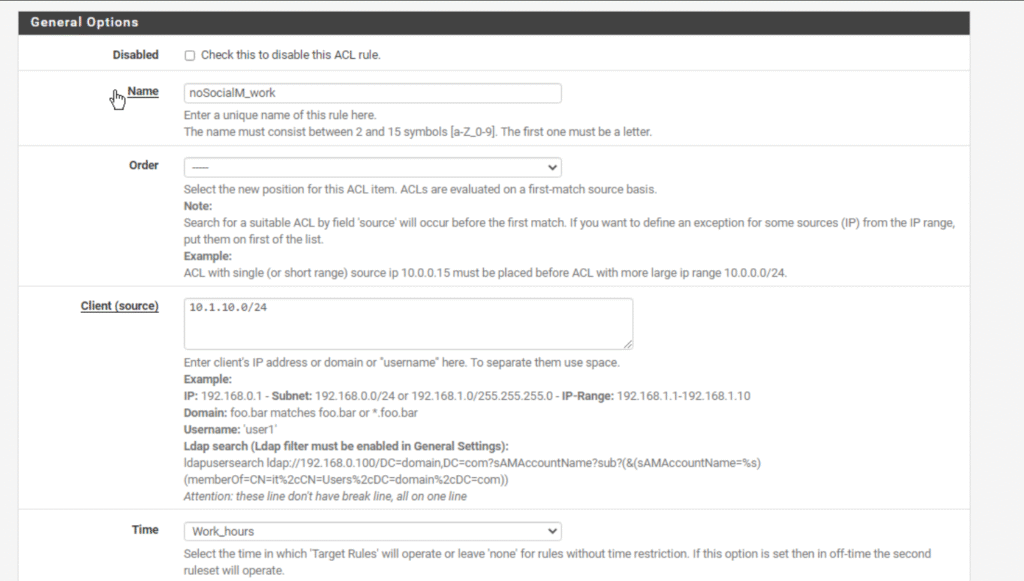

By implementing this ACL, users will not be able to reach social media platforms, helping to enforce organizational policies on internet usage, especially during defined times like work hours.
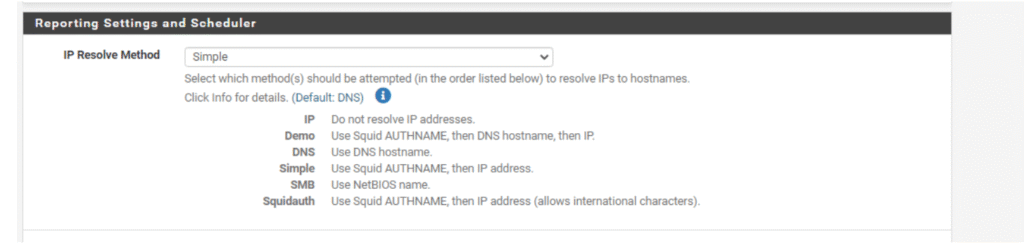
Configuring Lightsquid in pfSense
Lightsquid is a web-based reporting tool integrated with pfSense that analyzes Squid proxy logs to provide detailed reports on web usage. It allows network administrators to monitor who accessed which websites, bandwidth consumption, and overall internet activity.
For configuration:
- Lightsquid runs its own built-in web server.
- You need to define the port number on which you want to access Lightsquid’s web interface.
- You can choose whether to enable HTTPS for secure access to the reporting interface.
- Authentication is required, so you must provide a username and password.
- You also select the type of view; for example, a “Simple” view shows usernames and corresponding IP addresses to track usage clearly.
This configuration enables secure, controlled access to comprehensive proxy usage reports, aiding in network monitoring and management.
WPAD (Web Proxy Auto-Discovery Protocol) Configuration
WPAD is a protocol used by client devices to automatically discover the URL of a proxy configuration file using DHCP and/or DNS methods. Once the client detects and downloads this configuration file, it executes it to determine the appropriate proxy to use for a specified URL.
In practical terms, WPAD tells a web browser which internet proxy to use when a user on a network requests a web page. More specifically, WPAD informs the browser where to find a WPAD.dat file that contains network proxy details. This protocol allows domain administrators to centrally manage and serve proxy configuration files.
When WPAD is enabled:
- Web browsers automatically retrieve proxy settings without manual configuration.
- Users do not need to enter proxy information manually.
- Proxy configuration changes can be centrally managed and propagated across the network.
- It simplifies managing multiple devices in an organization by automating proxy setup.
WPAD is widely supported by modern browsers and is particularly useful in enterprise environments to streamline proxy configuration and ensure consistent policy application.
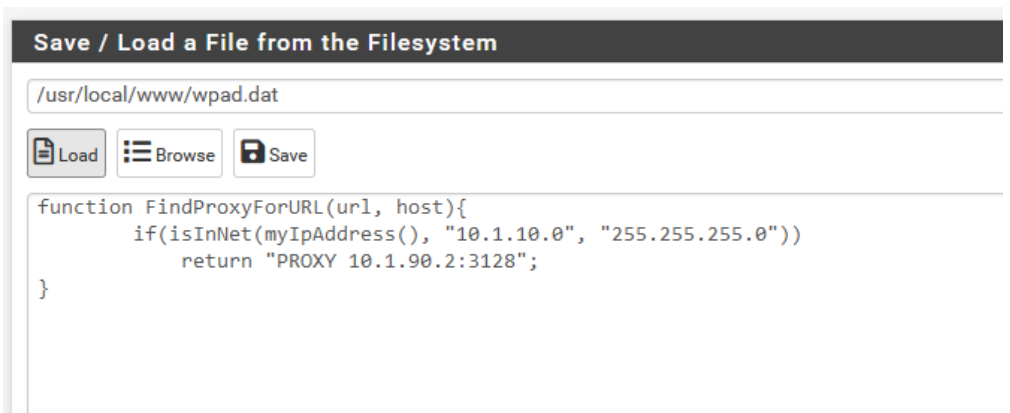
If my IP address in the range of 10.1.10.0/24 means using a proxy.
Conclusion:
Using Squid as a caching proxy within pfSense provides a robust solution for managing and optimizing internet access in network environments. Squid accelerates web browsing by locally caching frequently accessed web content, reducing bandwidth usage and improving response times. Integrated tools such as SquidGuard empower administrators to enforce granular access controls, filter content using predefined blacklists, and schedule access restrictions based on organizational policies. ClamAV integration enhances security by actively scanning web traffic for malware, while Lightsquid offers insightful reporting on user activity and bandwidth consumption.
This complete ecosystem—from caching to filtering, authentication, antivirus scanning, and detailed monitoring—enables efficient, secure, and policy-compliant web access management, especially suited for enterprise networks. Together, these components provide layered control and visibility that support productivity, security, and governance needs effectively.

Leave a Reply