This lab series guides you from the initial deployment of pfSense. Then, it progresses to advanced configurations. It provides a structured, step-by-step journey through every major feature. If you missed any of the other parts, they are linked below. This way, you can catch up and get the most from the full lab experience.
- pfSense Series: Simple Setup & Introduction
- pfSense Lab Part 2: Master pfBlockerNG Package
- Deploying pfSense: Complete Lab Series Part 3 – IDS/IPS With Snort
- pfSense Lab Part 4: Captive Portal with AD
- Secure Your Network with pfSense and Squid Proxy
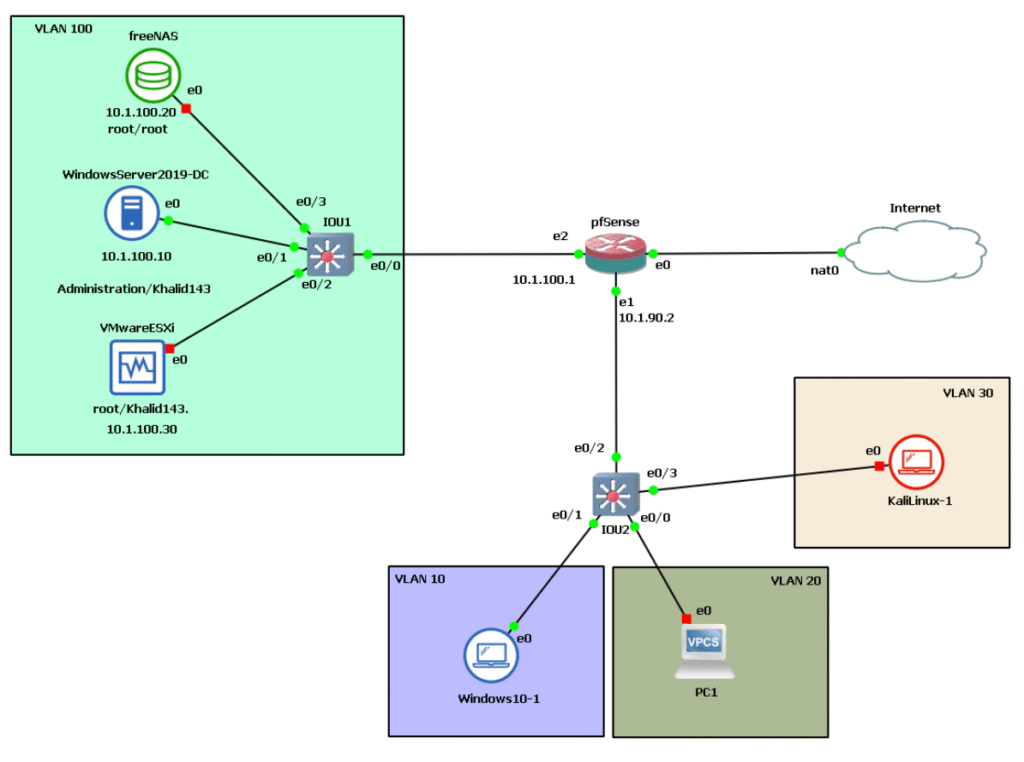
As a reminder, here’s the architecture below we’re working with.
Extending pfSense with Packages
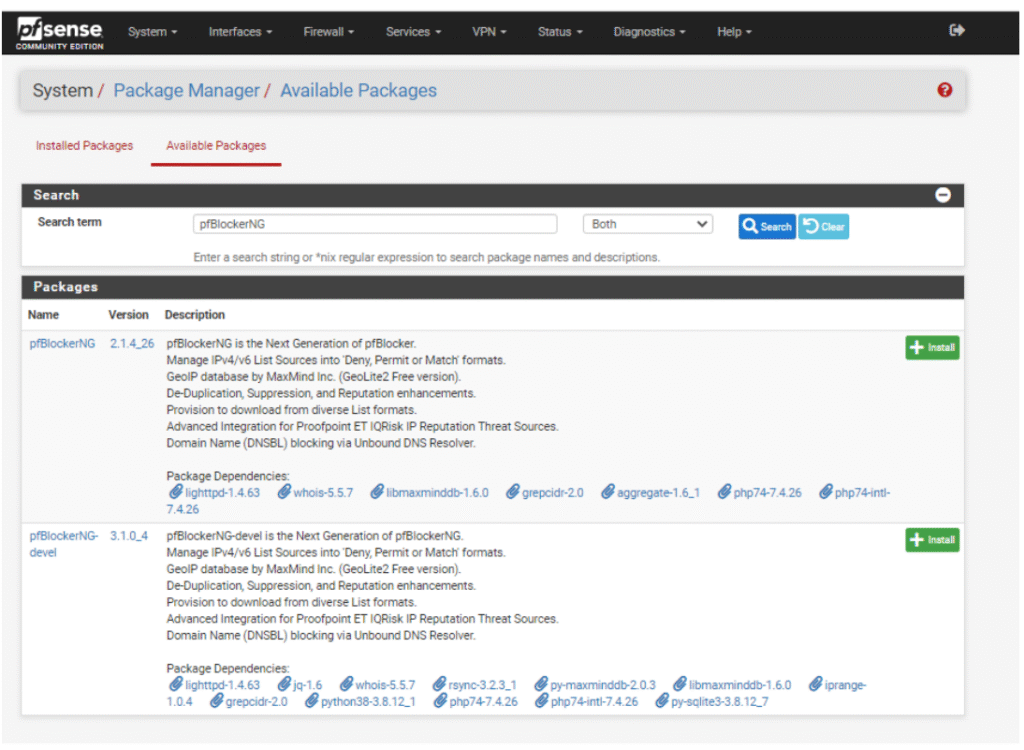
pfSense comes with a rich set of built-in networking and security capabilities, but one of its greatest strengths is its ability to be expanded through packages. These optional add-ons allow administrators to enhance the system by adding advanced monitoring tools, filtering services, or specialized network controls. All package installations and updates are handled directly through pfSense’s intuitive WebGUI, simplifying the management process even for complex features.
Packages are carefully curated and verified by Netgate, pfSense’s official parent company, to ensure reliability and security. This means that administrators can confidently deploy additional components knowing they are fully supported and regularly maintained to stay compatible with pfSense’s latest releases.
pfBlockerNG: Network-Wide Protection and Filtering
One of the most popular and powerful pfSense packages is pfBlockerNG, an open-source add-on developed to protect your entire network from malicious and unwanted content. It extends pfSense into a network-wide security and privacy firewall by blocking ads, tracking systems, and dangerous connections before they ever reach your devices. Beyond security, it also improves performance by reducing unnecessary traffic and optimizing bandwidth consumption.
pfBlockerNG uses a powerful feature known as DNSBL (Domain Name System-based Blackhole List) — a method that intercepts and blocks DNS requests to known malicious or advertising domains. In simple terms, when a device in your network tries to access a harmful or intrusive domain, pfBlockerNG intercepts the request and “blackholes” it, preventing the connection.
Key Features of pfBlockerNG:
- IP Blocking: Blocks specific IP addresses or networks known for spam, malware, or other threats.
- DNS Filtering: Ensures that requests to harmful or unwanted domains never resolve.
- Inbound and Outbound Traffic Filtering: Monitors both incoming and outgoing network flows to prevent data leakage or malware downloads.
- Rule-Based Routing: Allows administrators to apply custom routing policies and fine-tune how traffic is processed.
- Malicious DNS Blocking: Stops connections to domains involved in phishing, ransomware, or tracking.
- Ad and Spam Filtering: Removes unwanted advertising and email spam efficiently.
- Whitelist Management: Enables certain trusted sites or IPs to bypass filters when needed.
- Safe Search Enforcement: Forces search engines to operate in safe-search mode for extra protection.
By deploying pfBlockerNG, networks gain a proactive defense system that continuously updates itself, automatically adjusting to new threats and keeping your environment safe — all with minimal administrative overhead.
Why Packages Matter
For professionals and learners alike, understanding pfSense’s package ecosystem is crucial. It transforms pfSense from just a router or firewall into a complete network security platform capable of DNS security, intrusion detection, content filtering, traffic analysis, and VPN access control. Whether in a corporate, educational, or home lab environment, adding the right packages like pfBlockerNG, Suricata (for IDS/IPS), or Squid (for proxy caching and filtering) allows you to tailor pfSense to your exact needs.
These integrations not only add functionality but also instill professional-level experience in real-world network design — where modular flexibility, security, and performance must coexist seamlessly.
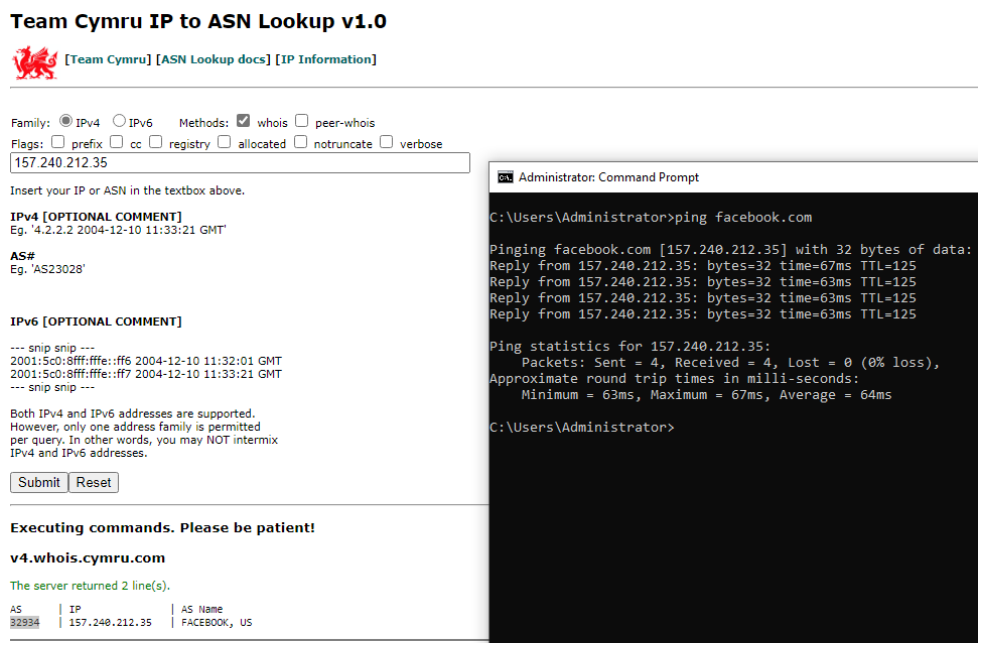
What is an ASN?
An ASN, or Autonomous System Number, is a unique identifier assigned to a large group of IP prefixes managed by a single organization or network operator (such as Facebook, known as Meta today). Every major service or corporation on the Internet operates one or more ASNs, providing structure and organization to how traffic is routed and identified globally.
The Procedure for Blocking Facebook
- Finding Facebook’s ASN:
To efficiently block Facebook, you first identify its ASN. For Facebook, the primary ASN is AS32934, as confirmed by multiple network lookup resources. This ASN covers the massive and frequently changing pool of IP addresses used by Facebook and its affiliated apps (Instagram, Messenger, WhatsApp, etc). - Network Query Example:
- First, you can “ping” a Facebook domain to see which IP responds.
- Then, use an ASN lookup tool such as asn.cymru.com or ipinfo.io to find out which ASN owns that IP.
- For Facebook’s main infrastructure, you’ll quickly identify AS32934.
- Implementing the Block with pfBlockerNG:
With the ASN in hand, you can configure pfBlockerNG on pfSense to deny all traffic associated with AS32934. This enforces policy at the network level regardless of domain, DNS tricks, or proxy avoidance — any IP advertised under Facebook’s ASN will be inaccessible to all users behind your firewall.
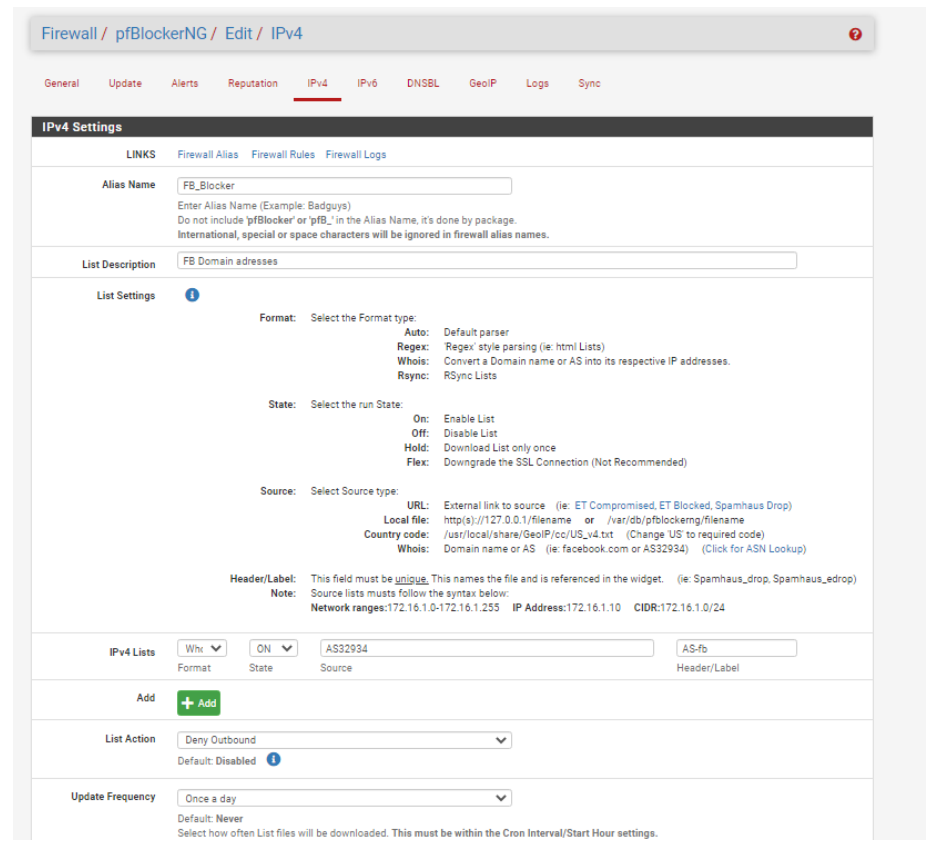
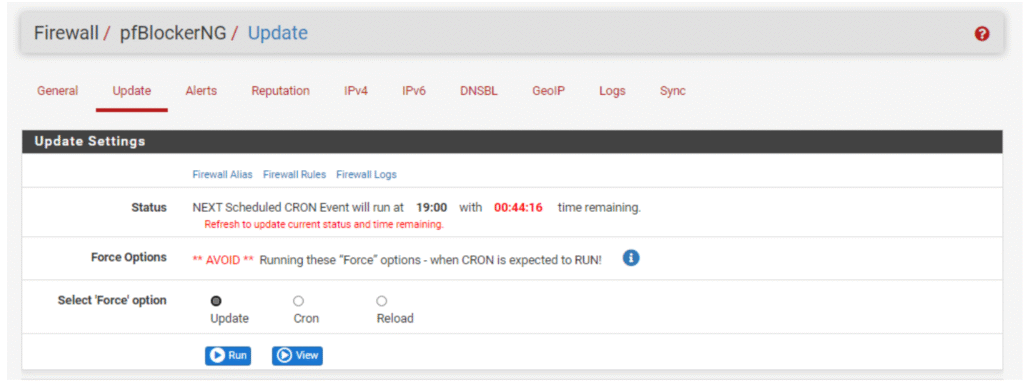
In the screenshot above, we have configured pfBlockerNG to block traffic based on the ASN (Autonomous System Number), specifically targeting outbound traffic to Facebook’s network infrastructure. The next crucial step is to update the settings to apply and confirm these changes across the firewall.
When checking the logs within pfBlockerNG, you will notice that it has successfully fetched all IP addresses linked to the ASN (Autonomous System Number) we previously specified. In this example, pfBlockerNG added 212 IP addresses to the blocked IP list.
This means that every time a device on your network attempts to access any of these IPs associated with the targeted ASN, pfBlockerNG will block the connection according to the configured policy. The logging feature records these blocked attempts, providing visibility into the effectiveness of your network filtering and enabling you to monitor potential access attempts to restricted services.
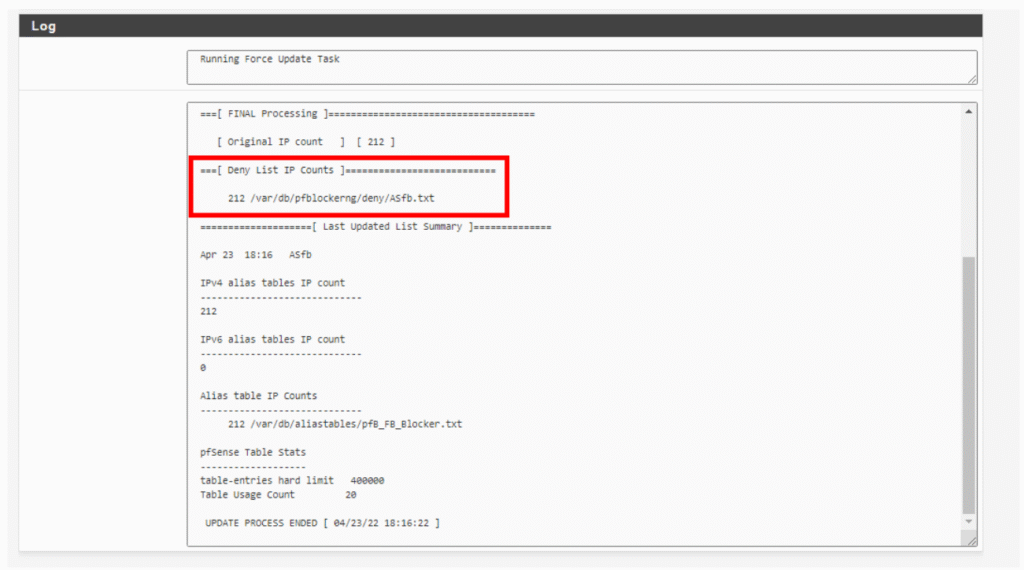
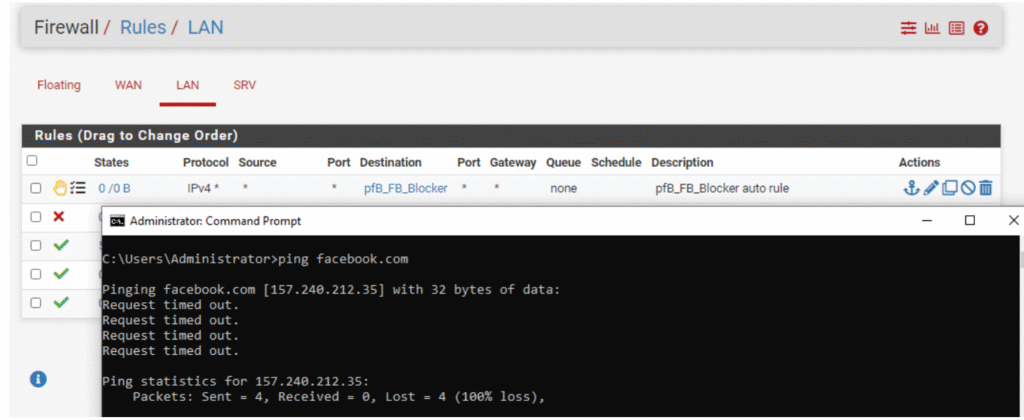
When reviewing the logs for pfBlockerNG, you’ll see that it has successfully retrieved all IP addresses associated with the ASN we specified earlier. In this case, 212 IP addresses have been added to the blocked list. These automatically generated rules are integrated into the pfSense firewall rule set, effectively preventing access as intended. After verifying from a Windows host within the network, you will find that access to those blocked addresses, such as Facebook IPs, is no longer possible. This confirms that the pfBlockerNG configuration is actively enforcing the intended network restrictions, enhancing security by blocking unwanted or harmful connections.
Conclusion:
This post highlighted the importance of leveraging pfSense’s package system to extend its core firewall and routing capabilities. While pfSense provides a solid foundation upfront, packages like pfBlockerNG significantly elevate network security by offering advanced features such as network-wide ad and malicious content blocking, ASN-based filtering, and automated updates of threat feeds.
Through hands-on implementation of pfBlockerNG, we demonstrated how it can actively protect an entire network by dynamically blocking IP addresses associated with specific Autonomous System Numbers (ASNs) like Facebook’s. This not only simplifies network administration but also significantly improves security and privacy by preventing access to unwanted or harmful services at the network level.
Leave a Reply
You must be logged in to post a comment.