This lab series guides you from the initial deployment of pfSense. Then, it progresses to advanced configurations. It provides a structured, step-by-step journey through every major feature. If you missed any of the other parts, they are linked below. This way, you can catch up and get the most from the full lab experience.
- pfSense Series: Simple Setup & Introduction
- pfSense Lab Part 2: Master pfBlockerNG Package
- Deploying pfSense: Complete Lab Series Part 3 – IDS/IPS With Snort
- pfSense Lab Part 4: Captive Portal with AD
- Secure Your Network with pfSense and Squid Proxy
Building robust, real-world-ready security from scratch is more than a configuration exercise—it’s an architectural journey. This series documents my hands-on experience deploying and customizing pfSense for an enterprise-grade network lab.
We’ll start from the big picture. We will delve into protocol-level security. At every step, we will use open-source tools and best practices.
Here’s an overview of the project’s architecture that we will be deploying.
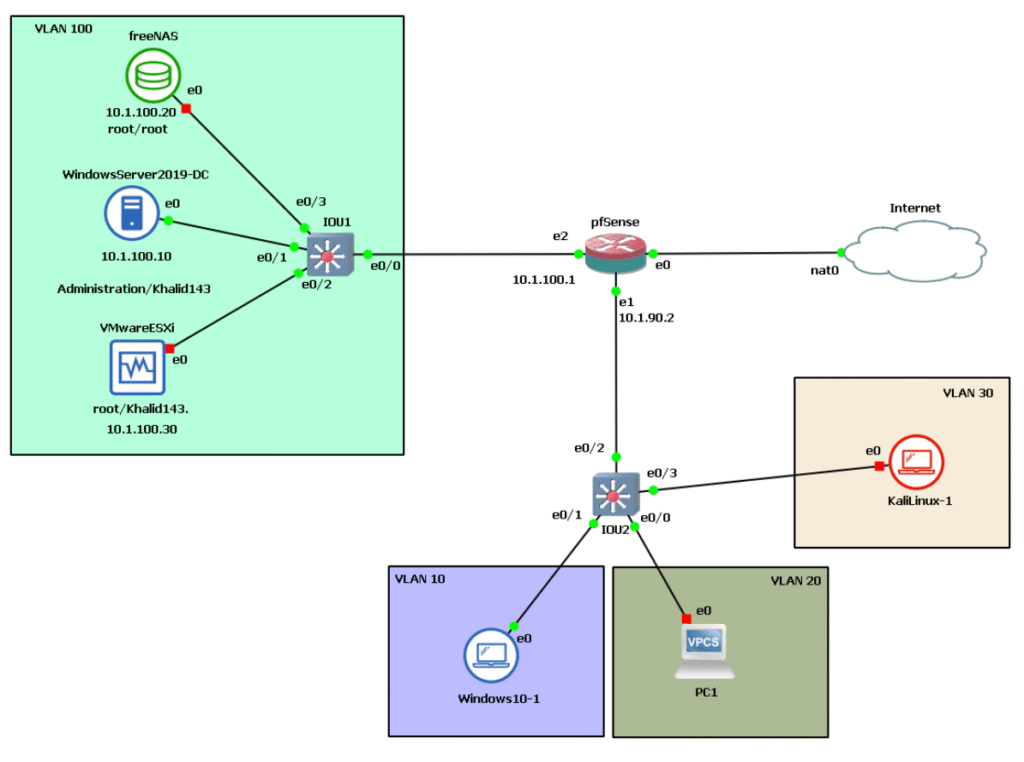
This architecture provides a clear, manageable foundation for anyone beginning their journey in networking and cybersecurity. Organizing the network into logical segments uses tools like pfSense and VLANs. This method separates critical servers, user devices, and testing machines into isolated areas. It helps you visualize real-world best practices. You can also understand how traffic moves safely through each part of your environment. This not only increases security but also keeps lab experiments safe and easy to troubleshoot.
For someone just starting out, working with this design helps you grasp the basics. You learn how different types of devices connect and communicate. These devices include servers, firewalls, and user workstations. It lets you practise securing resources, managing user access, and testing new tools in a sandbox environment. You gain hands-on experience you can build on. You are not overwhelmed by unnecessary complexity. This approach prepares you for more advanced work while helping you master practical skills step by step.
To carry out our project, we used two platforms (GNS3 and VMWAR). We used the first platform to design the architecture. It also helped create the interconnections. We used the second platform to set up and configure the virtual machines.
GNS3
- Graphical Network Simulator-3 (abbreviated as GNS3) is a network software emulator. It allows the combination of virtual and real devices to simulate complex networks. Initially developed to use the Dynamips emulation software to simulate Cisco IOS, it is open source.
- Dynamips can emulate the hardware of Cisco series routing platforms by directly booting a real Cisco IOS software image into the emulator.

VMware Workstation
- VMware Workstation is a virtualization platform that allows multiple operating systems to run on a single physical machine simultaneously.
- VMware Workstation supports bridging existing host network adapters and sharing physical hard drives and USB devices with a virtual machine. It can simulate disc drives; an ISO image file can be mounted as a virtual optical disc drive, and virtual hard drives are implemented as .vmdk files.

What is pfSense? Why Should You Use It?
The pfSense project is a free, open-source, custom distribution of FreeBSD designed to be used as a firewall and router, fully managed through an easy-to-use web interface. This web interface is known as the Web-Based GUI Configurator, or WebGUI for short. The pfSense software is a powerful and flexible firewall and routing platform. It also includes a long list of related features. The pfSense package system allows for additional scalability without adding bloat and potential security vulnerabilities to the base distribution.
pfSense can be configured as a stateful packet-filtering firewall, LAN or WAN router, or VPN appliance. It can also serve as a DHCP server or DNS server. Additionally, it can be used for other applications and special purposes.
Available next-generation pfSense security features:
- Stateful packet-filtering firewall or pure router
- Gateway-based and rule-based policy routing for multiple WANs, failover, and load balancing
- Transparent Layer 2 firewall
- Support for IPv6, NAT, and BGP
- Captive portal with MAC filtering, RADIUS support, and more
- VPN: IPsec, OpenVPN, site-to-site, site-to-client, site-to-cloud, and cloud-to-cloud, cloud connection assistant for Amazon AWS.
- Dynamic DNS client
- DHCP server and relay functions
- PPPoE server
- Reporting and monitoring features with real-time information
- Optional add-on packages such as snort or suricata for IDS/IPS and network security monitoring, Squid for optimized content delivery, and SquidGuard for anti-spam/anti-phishing and URL filtering
- And many more available!
Why use pfSense and not one of the standard routers?
A standard router is unreliable, has limited functionality due to manufacturer lock-in, and potentially has multiple software vulnerabilities. Manufacturers of basic routers have no incentive to fix software bugs, performance issues, or even serious security flaws.
Once the router is sold, the manufacturer has no incentive to continue spending money on development and security.
Implementing pfSense
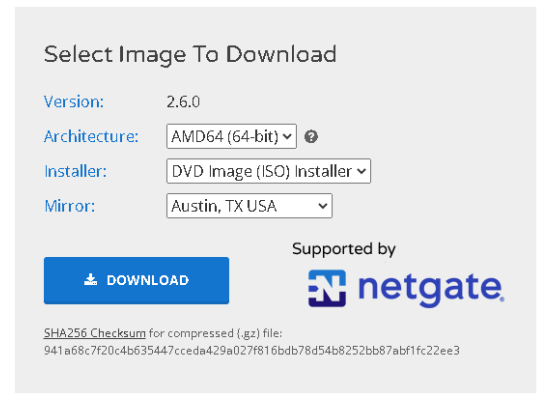
We can download pfSense Community Edition from the official website at https://pfsense.org/download/ after choosing the correct architecture model and installer.
The installation is straightforward. First, create a new virtual machine in VMware. Then, set up the appropriate hardware configuration for it to work.
The actual installation of pfSense involves choosing the keymap selection. The partitioning step selects the file system for the firewall’s target disc (which also includes the pool/disc type. In our case, ZFS supports multiple discs in various ways for redundancy and/or additional capacity.
Interface Assignment
When configuring pfSense, one of the foundational steps is interface assignment. If the firewall can’t automatically map your physical or virtual NICs, you’ll see a prompt (the Interface Assignment Screen). Here, you designate each network adapter’s role. The WAN is for internet access. The LAN is for the local network. Any OPT interfaces are for additional subnets or VLANs. This process ensures clear separation between internet-facing and internal traffic, and lays the groundwork for secure segmentation and policy enforcement
Think of your firewall as a smart traffic manager. It needs to know which cables or network cards connect to different areas.
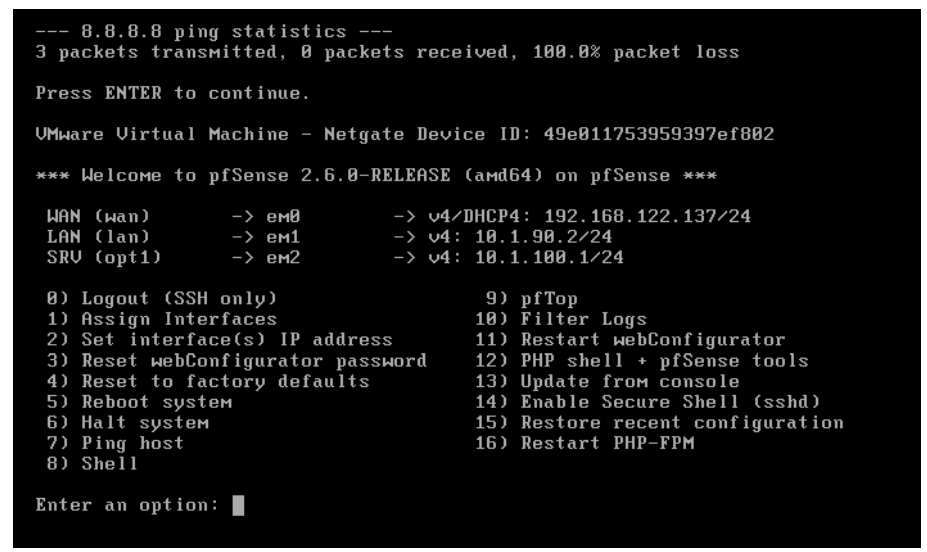
In my case, em0 is assigned as a WAN interface, which gets its IP address from NAT using DHCP, while em1 and em2 are configured manually.
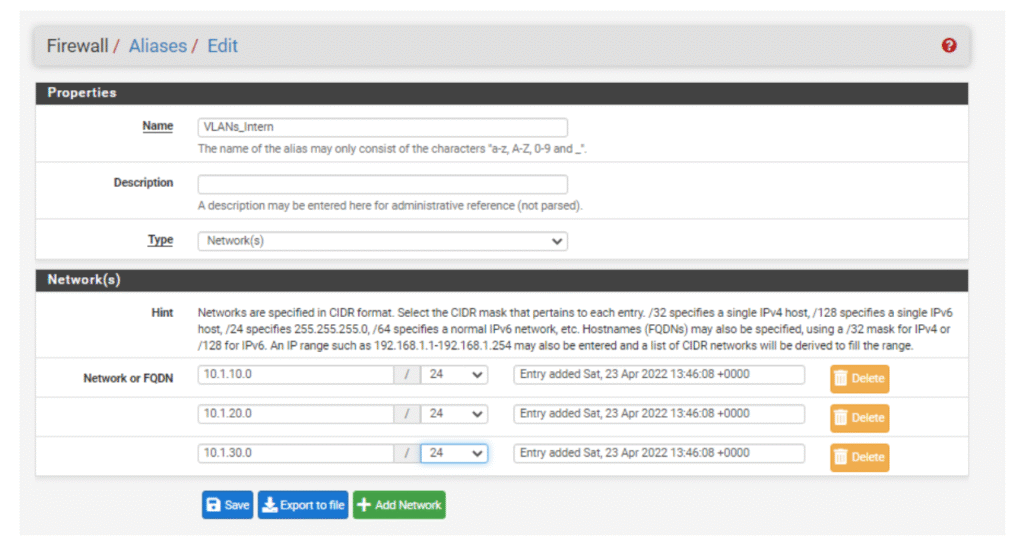
Creating Aliases to VLANs
In pfSense, aliases are a powerful abstraction that allows you to reference multiple addresses, networks, or ports with a single, readable name. By creating aliases for your VLANs, you dramatically simplify your firewall rules: a single logical alias replaces long lists of IPs or networks, making your policy sets concise, self-explanatory, and easier to manage as your environment grows. In this lab, aliases to VLANs are used to direct packets efficiently to their intended internal segments, enhancing both clarity and operational security.
Think of an alias as a label you give to a group of similar things—like naming all your work laptops “Staff PCs”.
What is a VLAN (Virtual Local Area Network)?
A VLAN (Virtual Local Area Network) segments a single physical network into multiple logical networks, allowing devices within each VLAN to communicate as if on isolated LANs. This separation enhances security, traffic management, and ease of administration. In pfSense, VLANs are configured by defining VLAN tags on parent interfaces, which then appear as virtual interfaces like OPT1 or OPT2. After creation, these VLAN interfaces can be activated, assigned IP subnets, and have firewall and DHCP rules crafted specifically for their traffic domains.
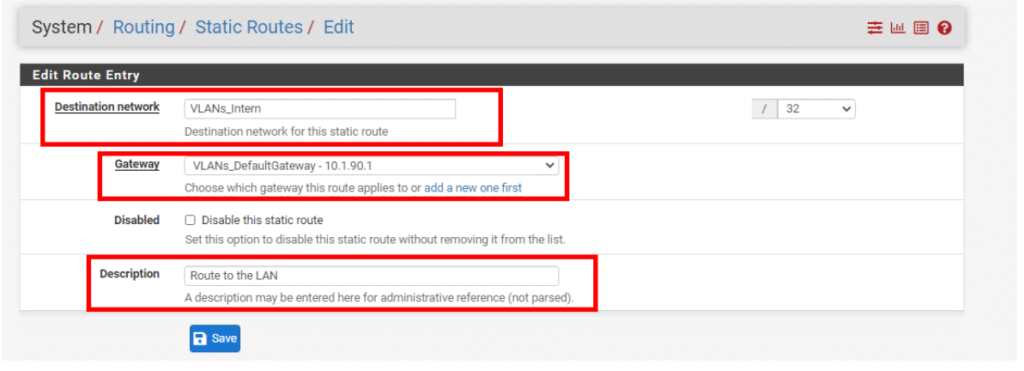
Once we’ve set up our VLAN aliases, the next critical step is making sure pfSense knows exactly where to send traffic meant for those internal networks. To accomplish this, we create a static route—a rule that tells pfSense, “if you see packets for this specific network, hand them off to this gateway.” In practical terms, this means adding a new default gateway pointing to our core switch. With this in place, pfSense is able to deliver packets efficiently to the VLANs we defined, keeping network traffic flowing smoothly and securely across all segments.
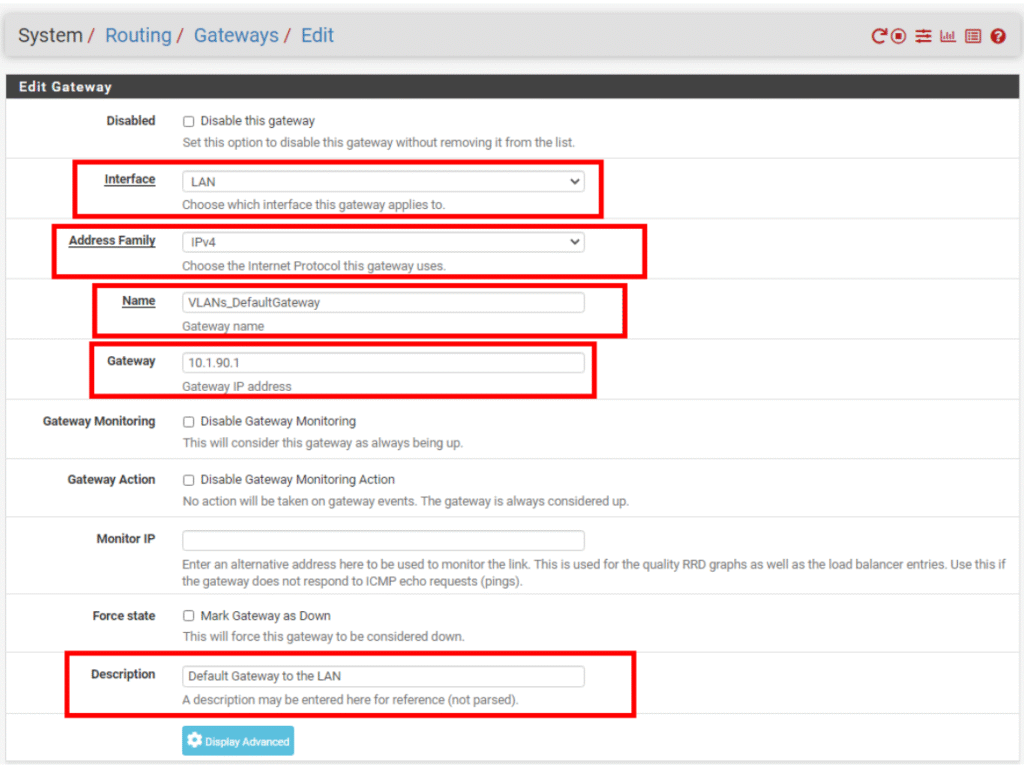
After successfully creating the new default gateway, the next step is to add a static route to the LAN. This static route tells pfSense exactly how to reach internal networks assigned to your VLAN aliases. Without these routing instructions, pfSense wouldn’t know where to forward packets meant for those VLANs. By specifying the destination network and linking it to the appropriate gateway (in this case, the internal switch), we ensure smooth and efficient traffic flow between pfSense and all devices within the LAN.
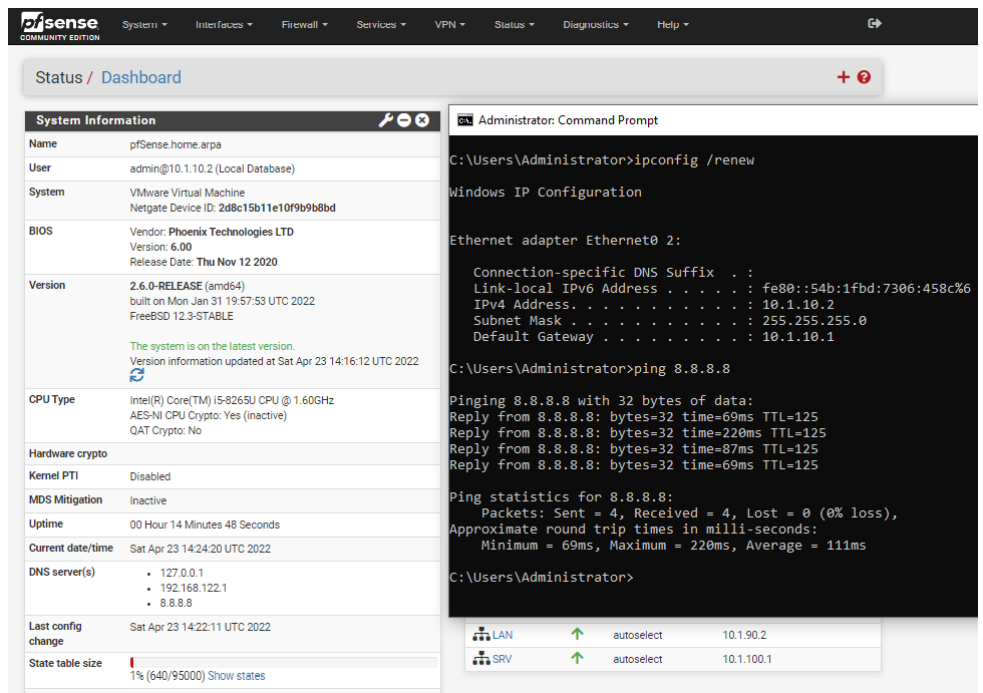
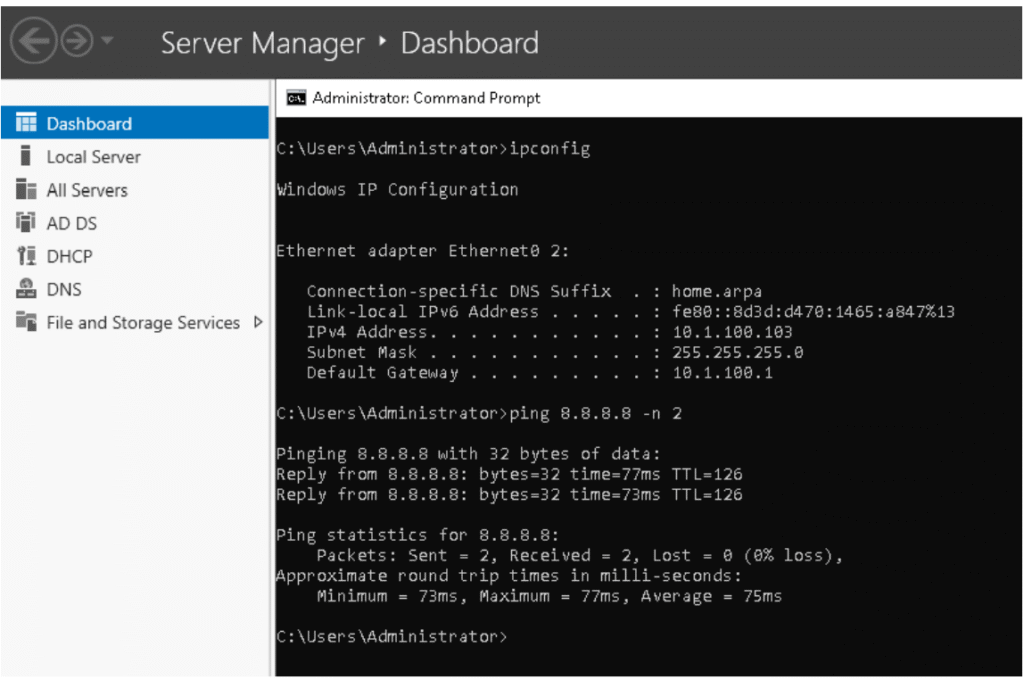
Verifying the Connectivity of Our Windows Host
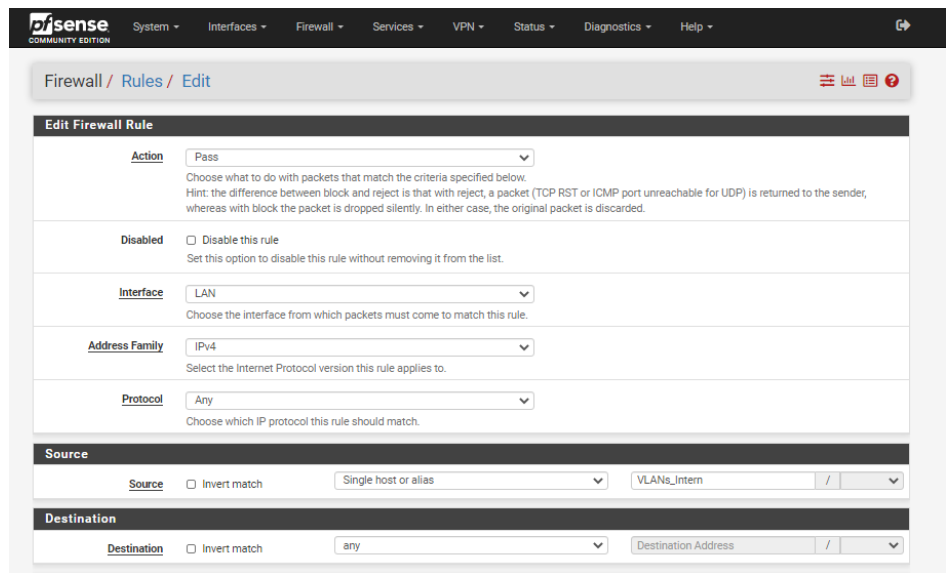
To verify connectivity for our Windows host, it’s essential to create a firewall rule that permits traffic from the VLANs to access external networks. This rule is a prerequisite before proceeding with any testing because it authorizes the firewall to allow outbound traffic from VLAN-assigned devices to the internet or other external resources, ensuring that clients can communicate beyond the local subnet.
Assign a new Interface to the Server zone
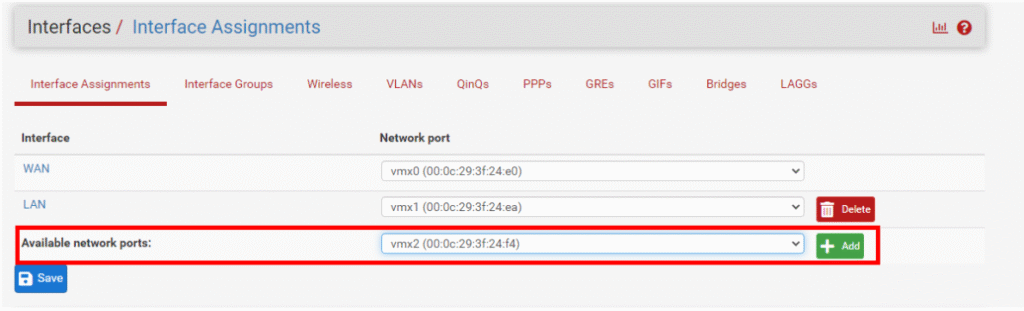
When you assign a new interface in pfSense, it appears in the list with a default name such as OPT1, OPT2, and so on, increasing numerically with each additional interface. The first two interfaces default to WAN and LAN but can be renamed for clarity. These OPT interfaces are accessible under the Interfaces menu, allowing you to configure settings specific to each interface by selecting them directly from the menu.
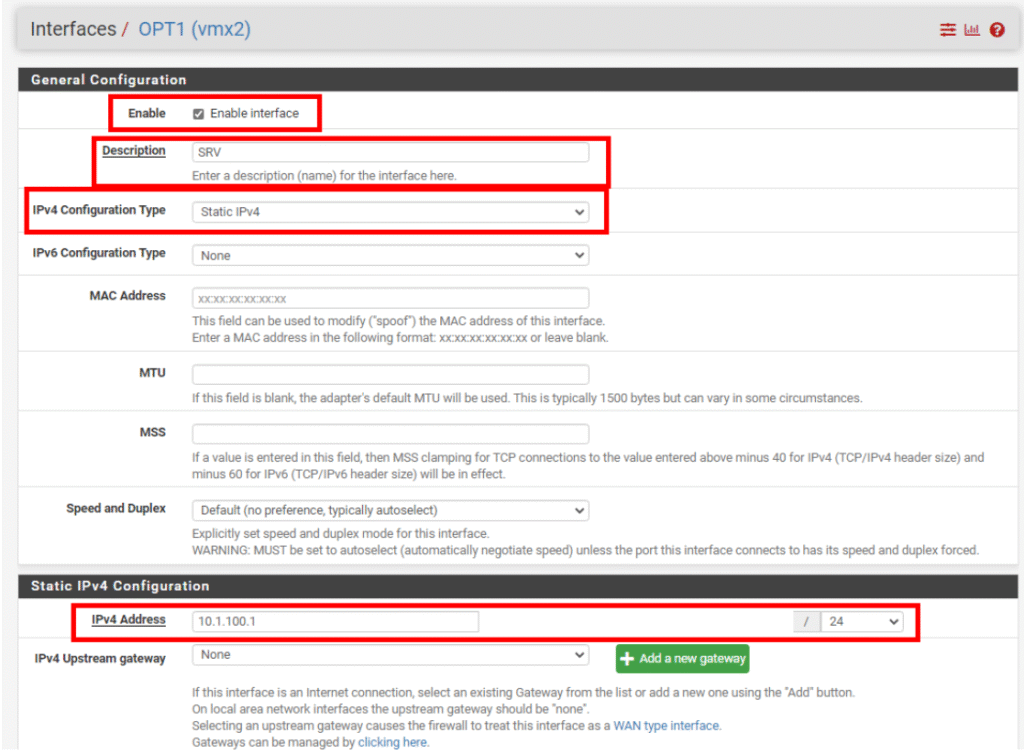
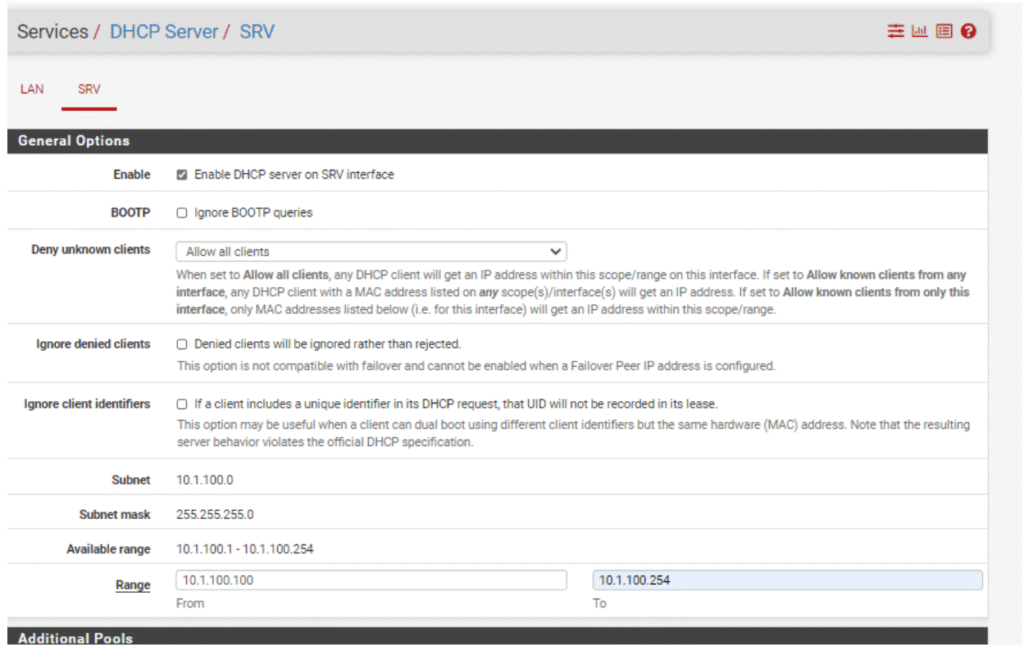
DHCP Configuration
Regarding the server zone, I wanted to configure the DHCP service on pfSense to automatically assign IP addresses to hosts. This means each device connecting to the server network will receive an IP address dynamically, simplifying management and ensuring devices can communicate without manual configuration.
Setting up DHCP on pfSense within the designated Interface allows the network to scale smoothly and avoids address conflicts, offering a practical solution for environments where devices frequently join or leave the network
What is DHCP (Dynamic Host Configuration Protocol)?
DHCP is a network protocol that automates the process of assigning IP addresses and other essential network settings to devices when they connect to the network. Instead of manually configuring each device with an IP address, subnet mask, default gateway, and DNS servers, DHCP handles this automatically. This is especially valuable in larger or dynamic networks, where devices frequently join or leave.
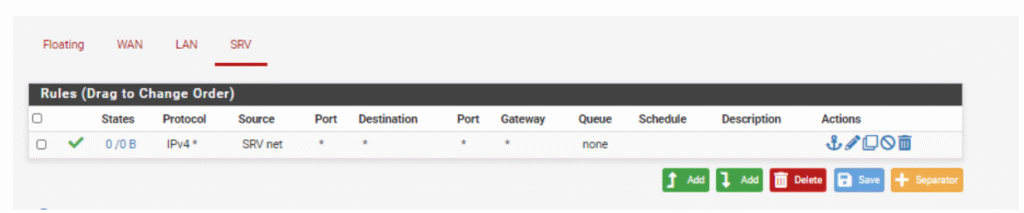
Similar to previous zones, the SRV (server) zone requires a dedicated firewall rule to permit outbound access to the internet. This rule enables devices within the SRV zone to initiate connections beyond the internal network, facilitating updates, remote access, and communication with external services while still controlling inbound traffic carefully through pfSense’s firewall policies.
Security Aspects
Management VLAN and ACLs
- A management VLAN is a dedicated virtual network segment that isolates all administrative and management traffic from the general user data traffic. The primary benefit of implementing a management VLAN is enhanced network security: by keeping management interfaces and protocols separate, unauthorized users find it significantly more difficult to intercept sensitive communications or make unauthorized configuration changes to network devices. This isolation acts as a safeguard, ensuring that only trusted administrators can access critical infrastructure components.
Implementing ACLs on the switch:
Disable access to the switch configuration from VLANs (and only VLAN 10 can access as a management VLAN).
Allow firewall access to the management VLAN only
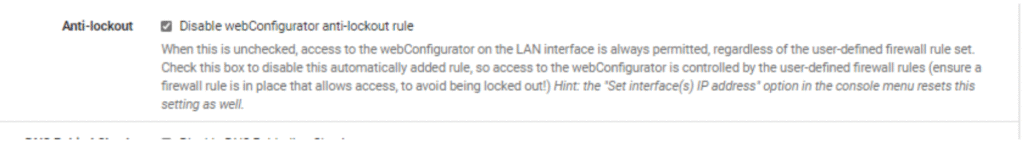
To limit access to a specific VLAN, we need to disable the anti-lockout rule,
which allows management access from any machine on the LAN and prevents firewall rules from being configured to lock the user out of the web interface.
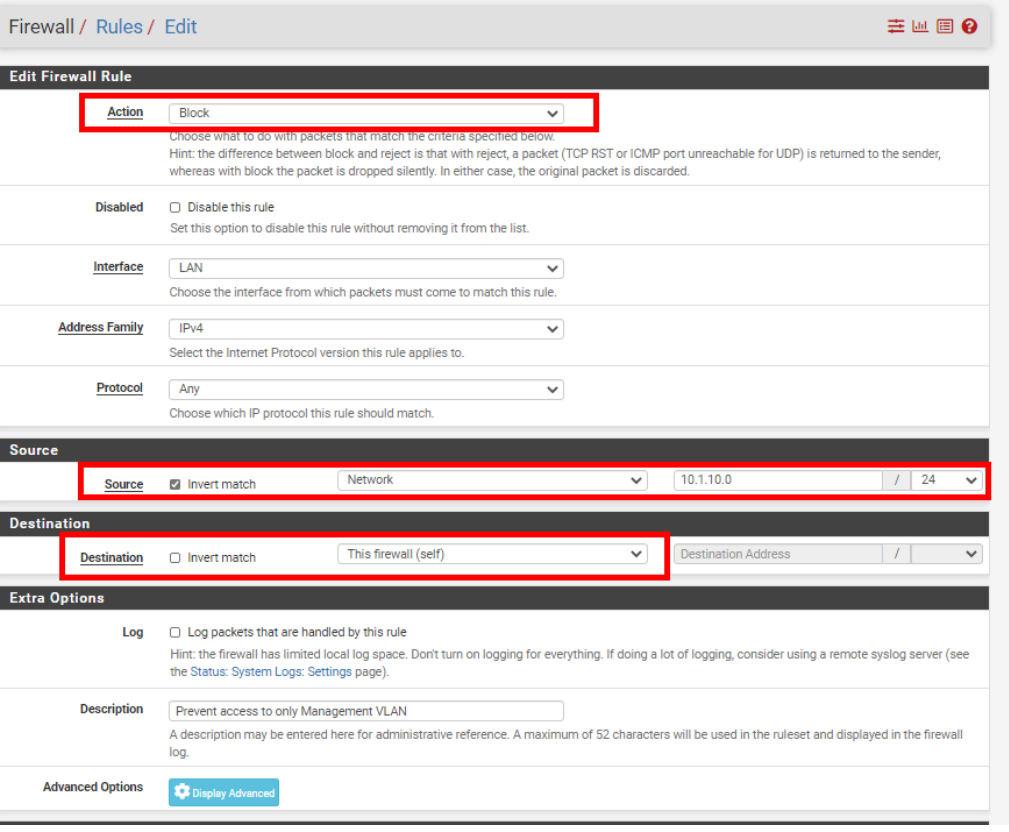
Next, we need to create a firewall rule that specifically grants access only to the management subnet. This ensures that administrative traffic is tightly controlled and limited to the designated VLAN, preventing unauthorized users or devices from accessing critical management interfaces. By restricting this access, we enforce a strong security posture, allowing only trusted administrators to manage network equipment and configurations.
This rule is vital in protecting your network infrastructure from unintended or malicious access, keeping management functions isolated and secure within their own virtual segment.
Conclusion
This post walked through the foundational steps of setting up a secure, segmented network environment using pfSense and VLANs. Beginning with interface assignment, we ensured the firewall knows how to handle different physical and virtual network connections. Creating aliases for VLANs allowed us to manage groups of addresses and ports more efficiently, while static routes enabled pfSense to direct traffic correctly across internal networks.
We explored configuring DHCP services for automatic IP address management, simplifying network administration and scalability. The importance of firewall rules for VLANs was emphasized, ensuring that each zone—be it user workstations or servers—has controlled access to resources and the internet. A key part of the security setup involved creating a dedicated management VLAN and implementing precise Access Control Lists (ACLs). Isolating management traffic this way significantly raises the network’s security posture by limiting access to authorized personnel only. Disabling the default anti-lockout rule and applying tailored ACLs further protects critical configurations.
Taken together, these steps provide a practical blueprint for anyone starting out with pfSense or network segmentation to confidently build secure, scalable, and manageable network infrastructures. This foundational knowledge will empower you to advance toward more complex configurations and real-world deployments with confidence.
Leave a Reply
You must be logged in to post a comment.